Get Ready to Meet Tomorrow’s Threats
At Atrity, we are specialized in offering next-generation security solutions that are rich in features including SSL/ SSH inspection, reputation-based malware filtering, active directory integration support as well.
The granular security policies help us to detect application-specific attacks and enable us to capture more malicious activity than traditional firewalls. We provide an array of cyber defences that work together to deliver integrated threat protection with application awareness, user identity, and content inspection with high performance and scalability.
Moreover, we deliver intelligence-enhanced threat protection, around-the-clock device health and security event monitoring, and management of changes, patching, and upgrades.
SERVICE OFFERINGS
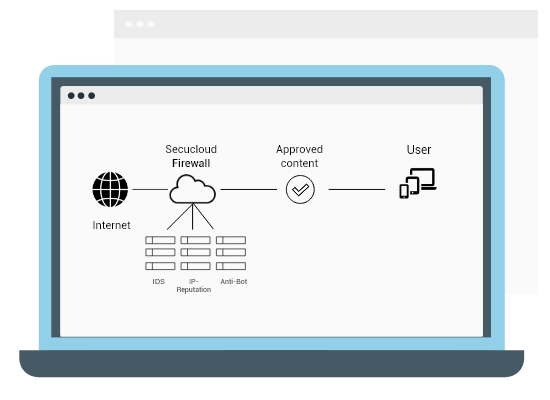
Next-generation Firewalls - Scan, to Avoid Spam
Protect your infrastructure with our real-time monitoring instilled with powerful threat intelligence.
You can completely rely on our security experts in firewall technologies and industry practices thereby retaining aspects of management as you prefer. Within the constraints of time, budget, technology and the set of requirements, we deliver real solutions that exceed expectations, excel anticipated outcomes and demonstrate measurable business success.

Some of the Networking solutions we provide are:
Build a strong networking infrastructure with Atrity and establish a hassle-free communicative space between your endpoints and users.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall
 Read More
Read More